Identity Protection
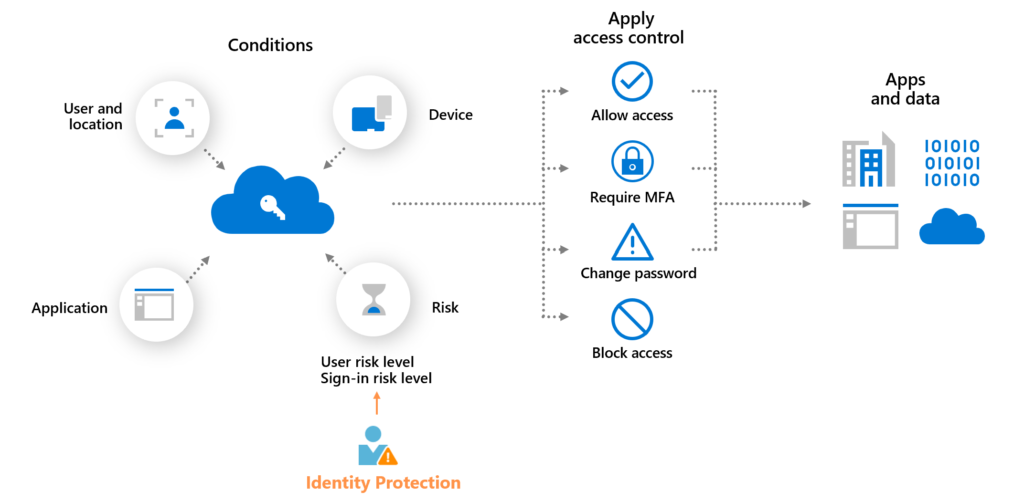
Azure AD Identity Protection enables us to add an intelligent layer to our authentication procedure. It strengthens our Conditional Access controls by associating risk categories with user credentials and sign-in attempts. For example, depending on variables like frequency, client device, or geographic location, we may analyse a specific sign-in request and determine the risk associated with it. The sign-up procedure might then take a new course of action based on the level of risk deemed appropriate.
Identity Protection detects risks of many types, including:
- Anonymous IP address use
- Atypical travel
- Malware linked IP address
- Unfamiliar sign-in properties
- Leaked credentials
- Password spray
- and more…
The risk signals may prompt remediation actions such as asking users to conduct multifactor authentication, reset their password via self-service password reset, or restrict access until an administrator takes action.
Risk-based access policies
When a sign-in or user is identified as being at risk, access control measures may be used to safeguard companies. Such policies are known as risk-based policies.
Sign-in risk and User risk are the two risk criteria offered by Azure AD Conditional Access. By establishing these two risk factors and selecting an access control strategy, organisations may develop risk-based Conditional Access rules. Identity Protection transmits to Conditional Access the risk levels it has identified at each sign-in, and if the criteria of the policy are met, the risk-based rules will take effect.
Creating a Risk Based Access Policy
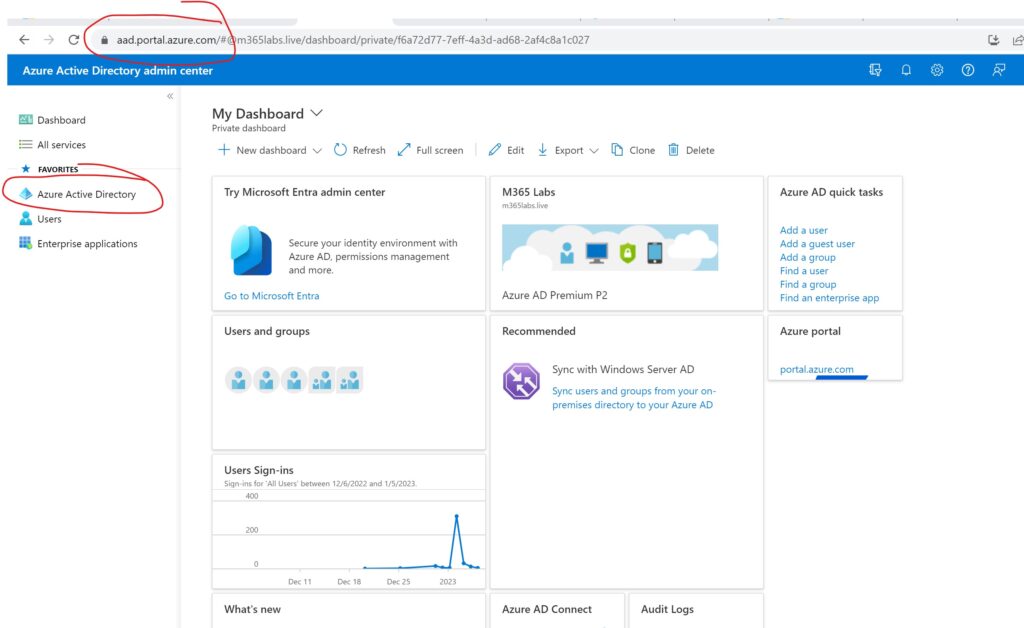
- Login to Azure Active Directory Portal https://aad.portal.azure.com with appropriate rights.
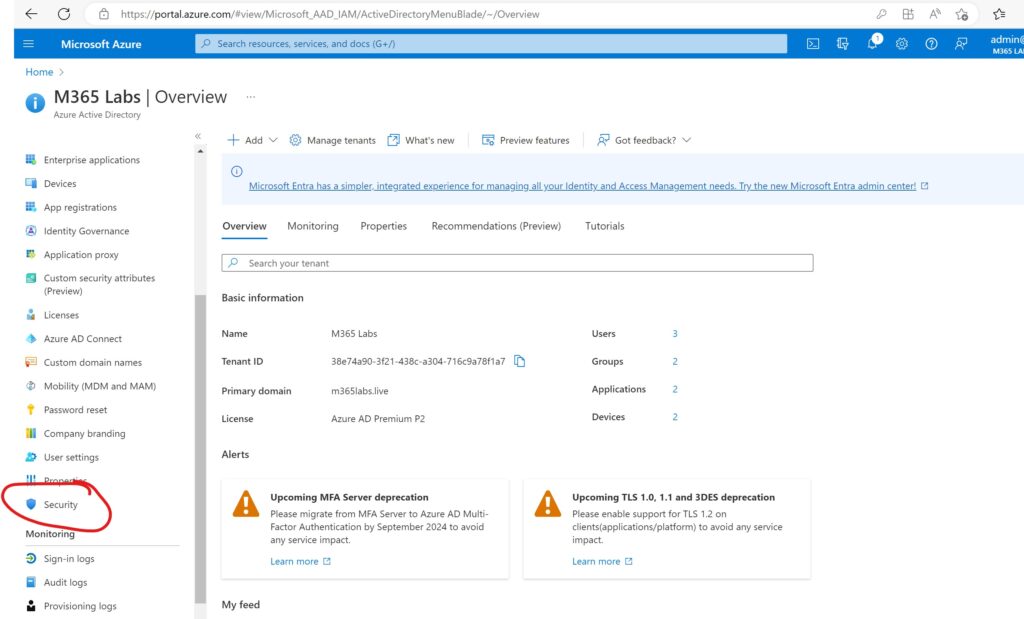
Click on Security
Click on Conditional Access
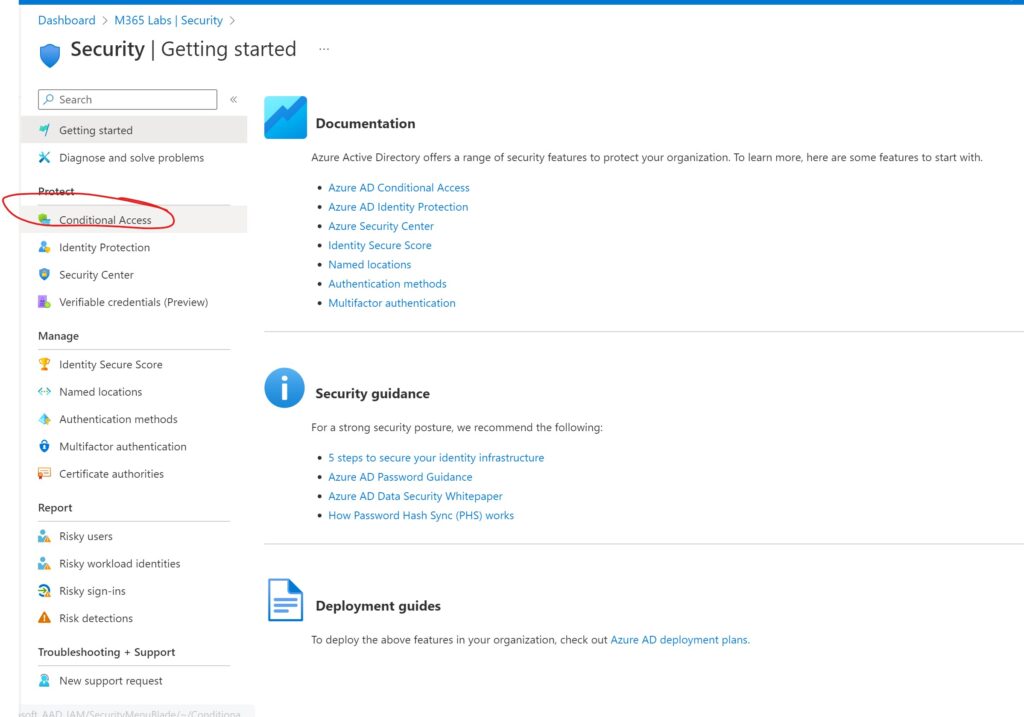
Select New Policy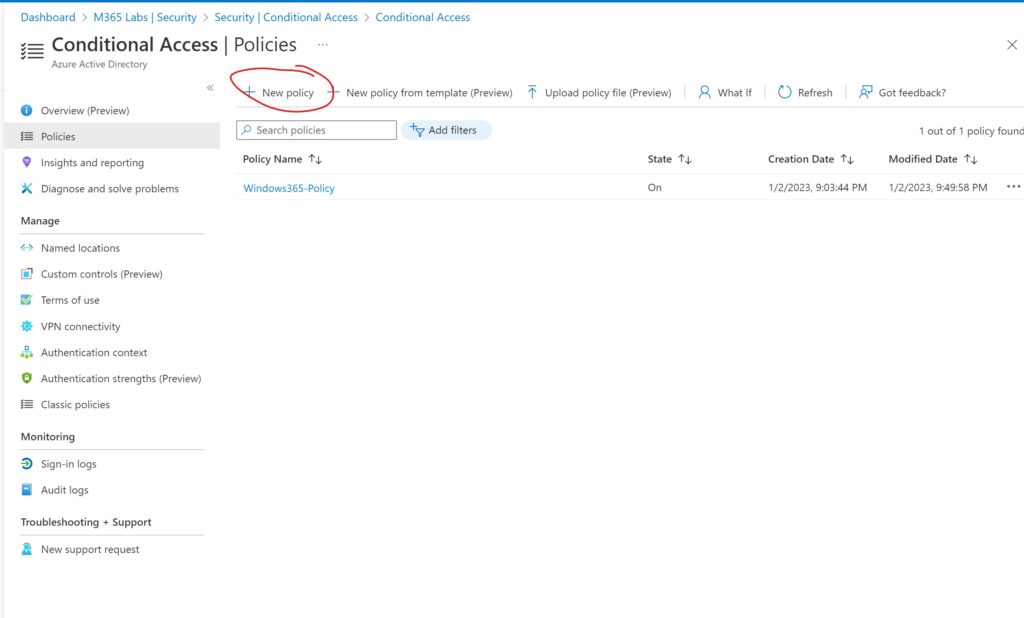
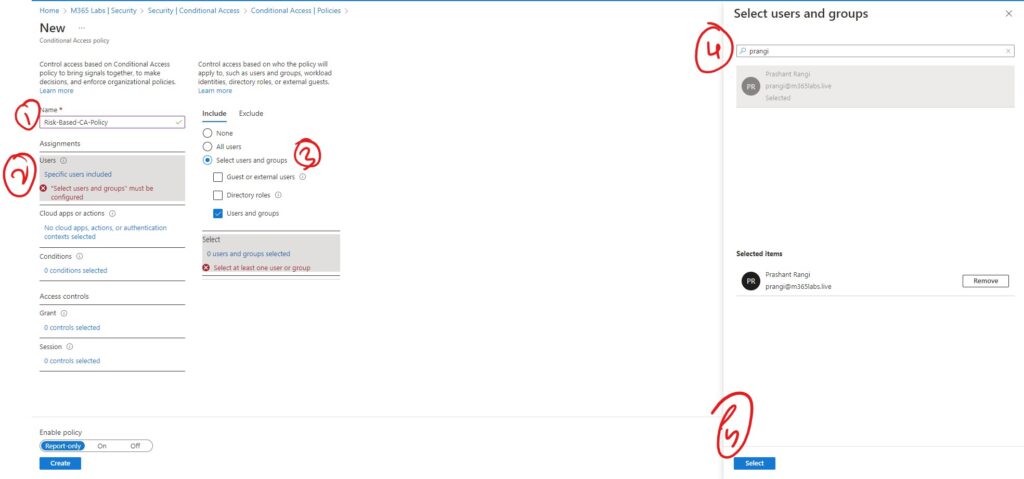
Type in the appropriate Name & select the user or group you are to assign this policy.
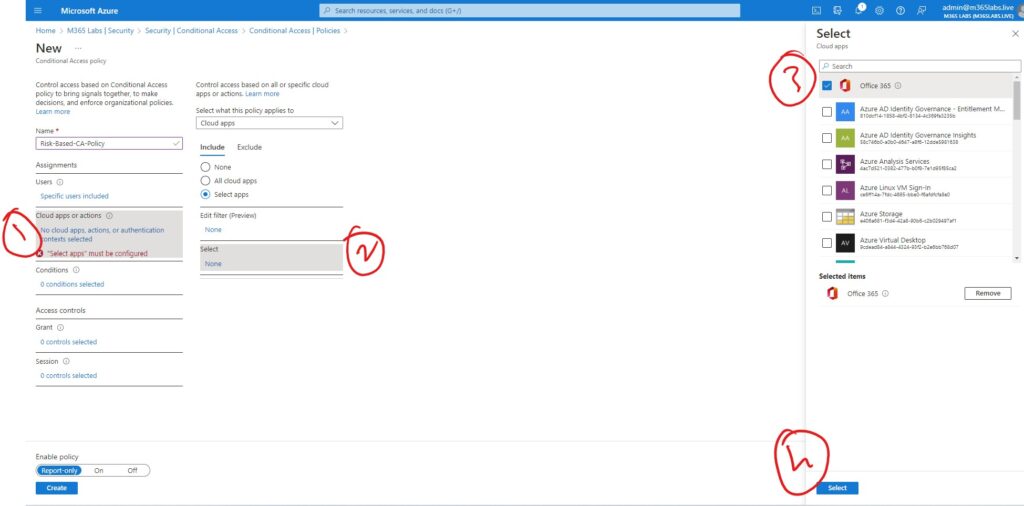
Select the application
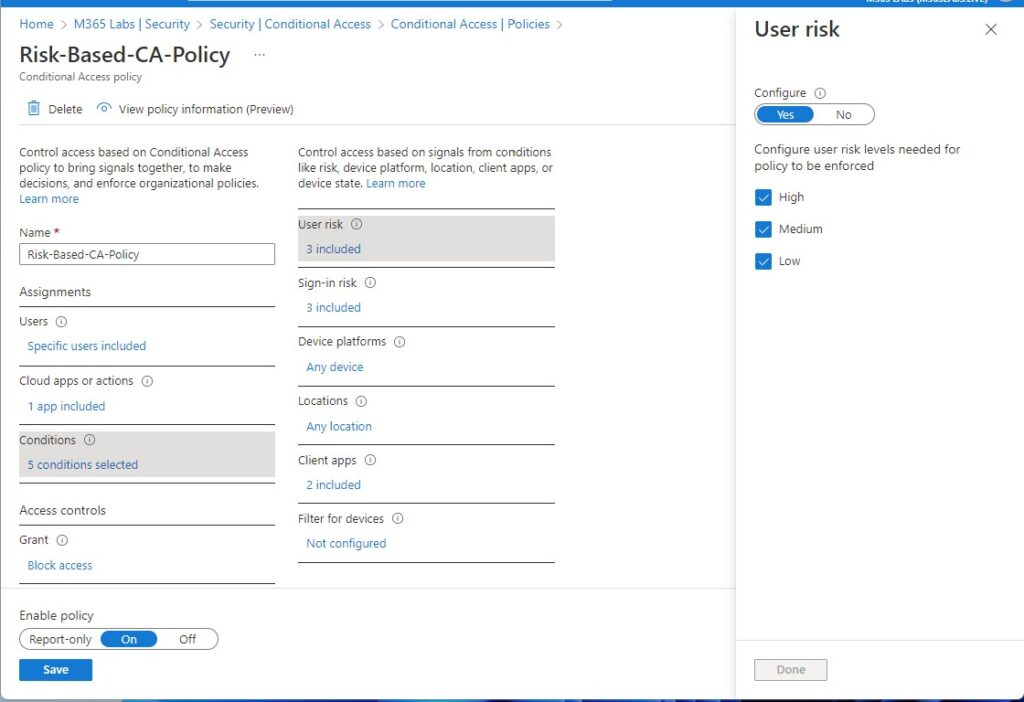
Select the User Risk Level, Sing-in risk level, Device Platform, Location & Client Apps.
Note : As we are creating a Risk based CA policy atleast select User Risk & Sign-in Risk
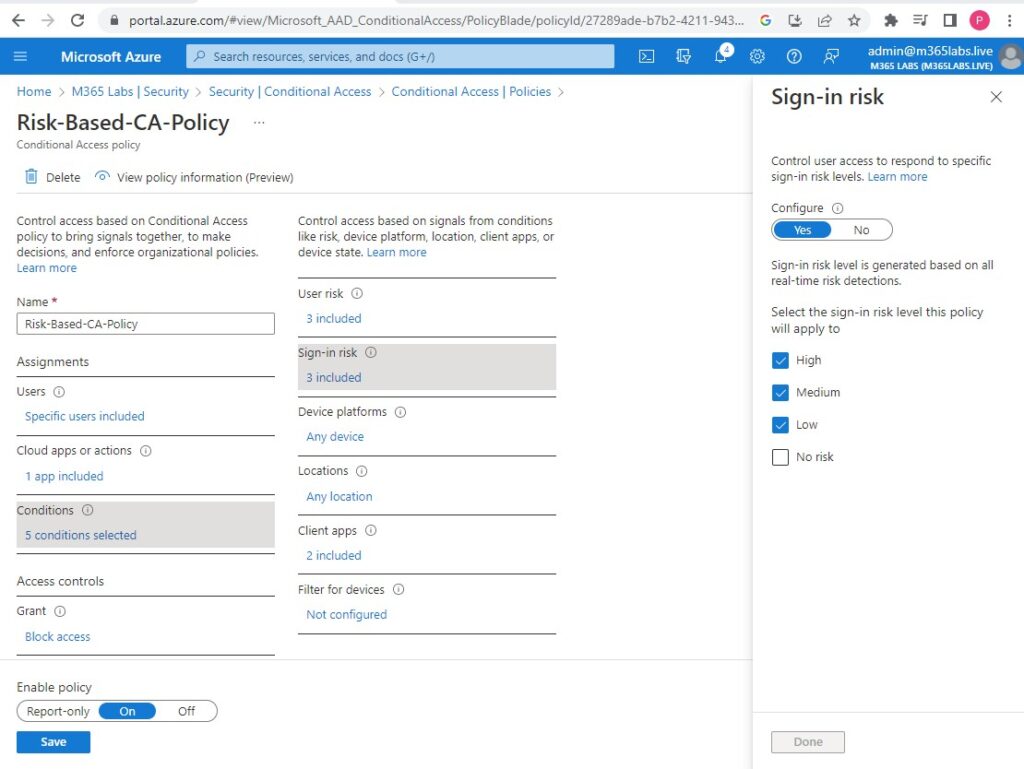
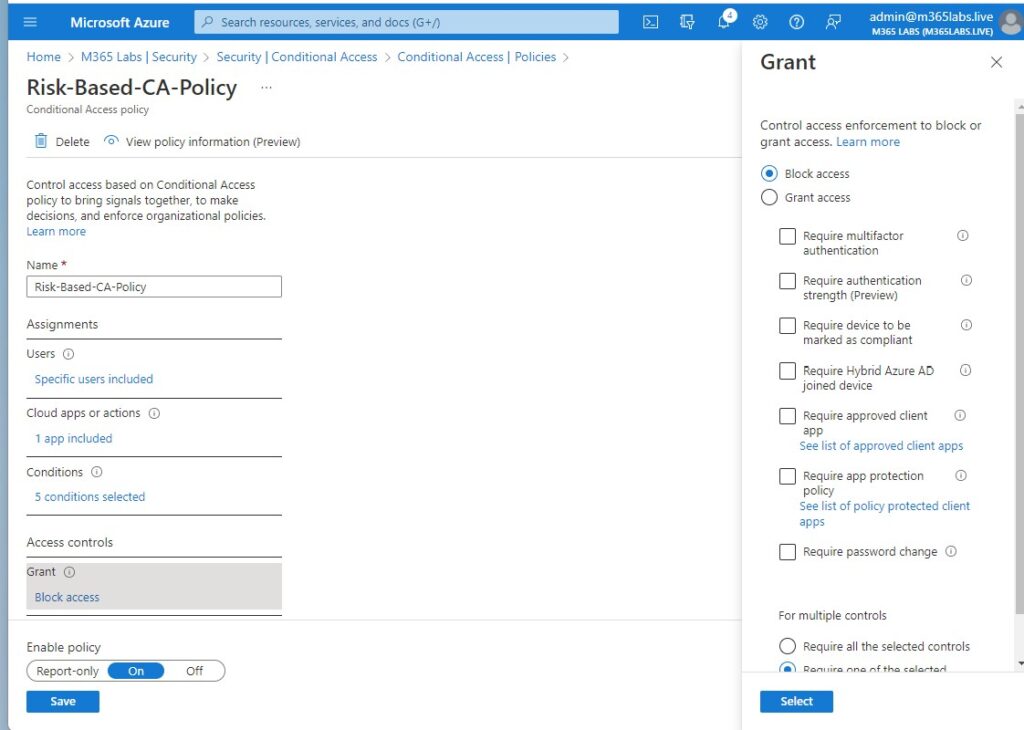
Select whether you want to Allow or Block access
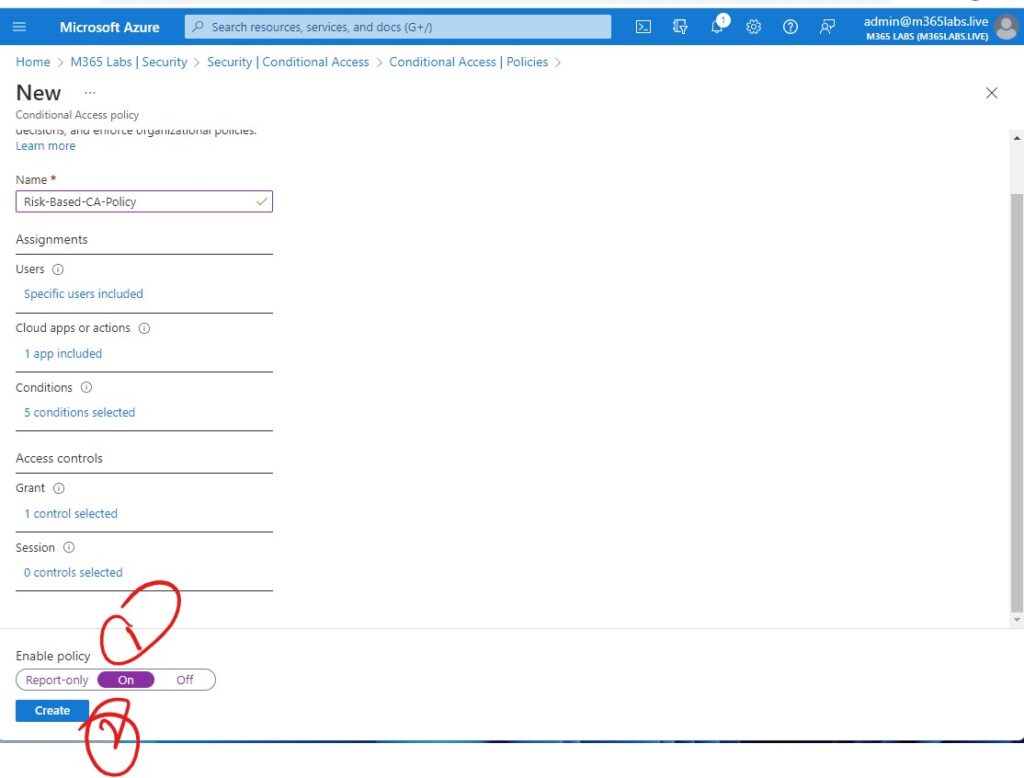
Enable the Policy & Click on Create
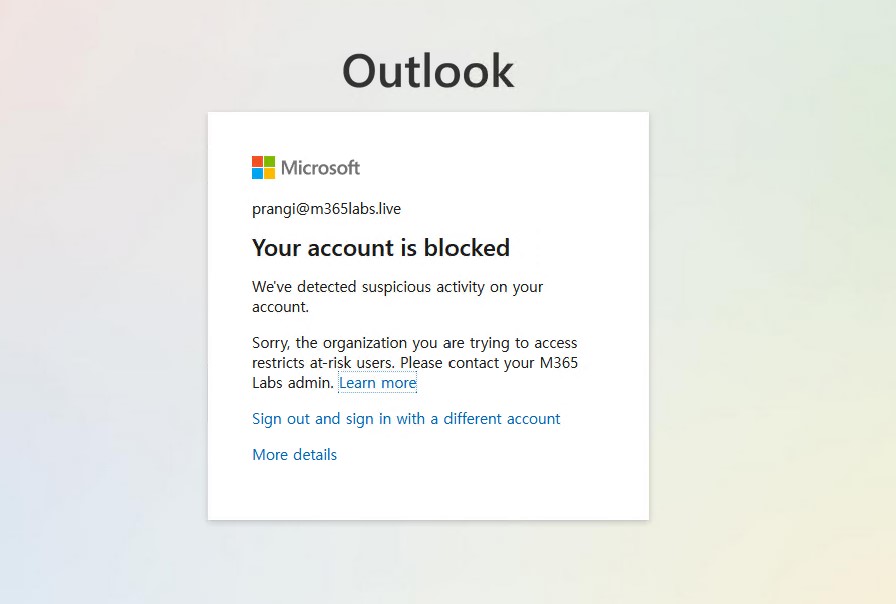
 Once you try to login
Once you try to login
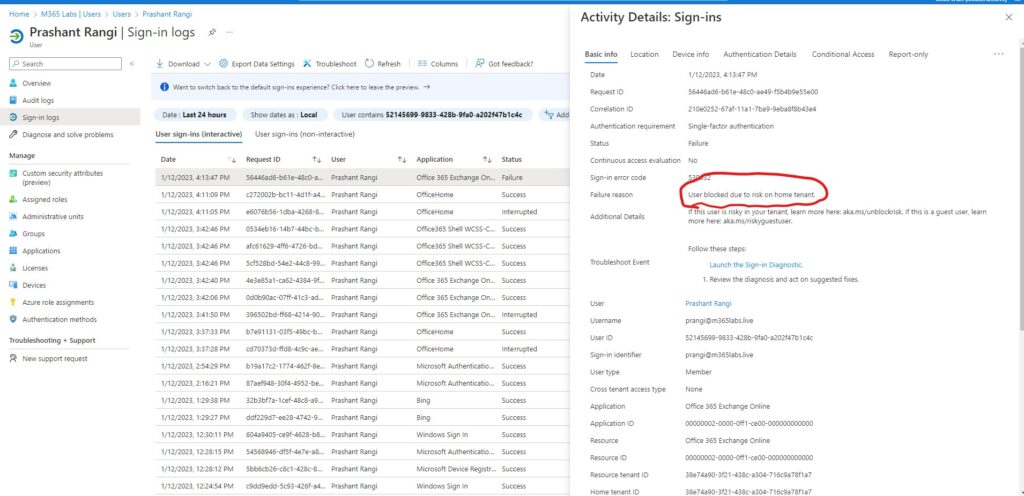
To validate, you can check the Sign-in logs of the user in Azure Ad.
Hope this will be informative for you. Please do share if you find worth sharing it.
